Social media is one of the most critical tools you can leverage to increase your brand awareness. It also lets you interact with your audience on multiple platforms and serve your customers better. Your target audience is most likely part of the 250 million social media users in the United States, so planning a social media strategy should be one of your priorities.
But social media isn’t just all about promoting your business. It also involves protecting your organization from cybercriminals who want to steal your data and money for their own gain. And don't think that small businesses are safe; they are actually more prone to cyberattacks, because their security defenses are much easier to penetrate. And because social media involves interacting with your customers, some people might hack your social media accounts to give you a bad reputation.
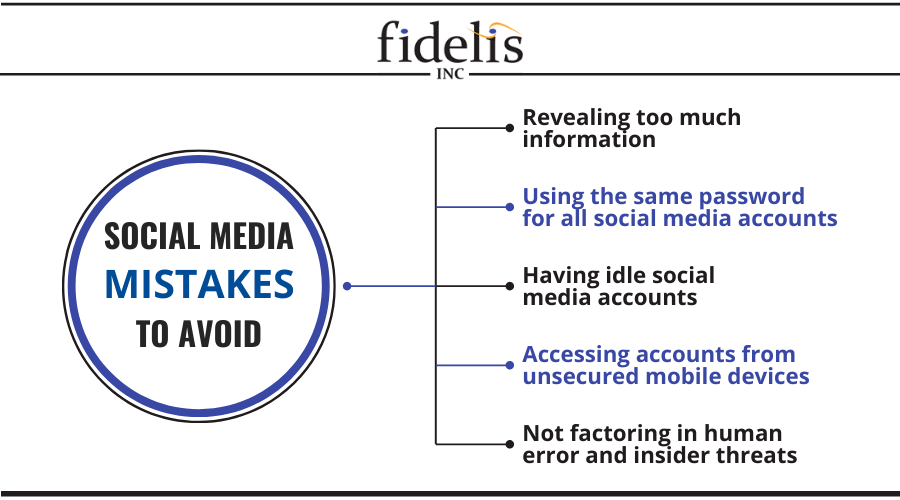
Here are some of the social media mistakes your small business should avoid:
#1. Revealing too much information
Take extra precautions when using social media to promote your business. When representing your company, avoid sharing personal information like your birthdate, current hometown, education, family members, and mobile number.
These data are enough for cybercriminals to commit identity theft against you and your business. For instance, they can launch phishing attacks where they pretend to be the company CEO to steal more information. This will ruin your reputation with your customers and with peers in your industry.
#2. Using the same password for all social media accounts
One of the biggest mistakes small businesses could commit is using the same password for all their social media accounts. If your Facebook account is hacked, for example, cybercriminals can easily take over your other accounts to lock you out, access all your private information, or damage your credibility with your audience.
Even high-profile social media accounts suffer because of the threat of account takeover. For instance, when the Associated Press’ Twitter account was hacked, cybercriminals sent out rogue tweets that caused panic around the United States. It also resulted in the Dow Jones plunging, undoubtedly costing people and businesses a significant amount of money.
If larger enterprises are struggling to prevent social media account takeover, your small business should be no exception. Use different passwords for your social media accounts, and ensure that they can’t be guessed easily. Change your passwords often to lessen the chances of future breaches. You can also choose to optimize your passwords by using a password manager, like the one offered by Google and LastPass.
Unsure how to protect your business?
Read our FREE eBook, 3 Essential types of cyber security solutions your business must have and find out how you can optimize your business's cybersecurity without spending too much.
#3. Having idle social media accounts
Being accessible on various social media platforms can be beneficial for your business, as it maximizes your exposure online. There will be some platforms, however, that you may not give a lot of attention to, especially those that don’t engage really well with your customers.
However, do not ignore your idle social media accounts because they could be targeted by cybercriminals. Unmonitored accounts might be hacked, and cybercriminals could defame your business by posting fraudulent and malware-laced messages that will threaten your followers’ security and reputation.
#4. Accessing accounts from unsecured mobile devices
Posting on social media only takes a few taps on a smartphone. But given this convenience and growing reliance on mobile devices, businesses need to ensure that these gadgets don’t fall into the wrong hands. For instance, if a company tablet gets stolen, anyone can take over your social media accounts and message your audience with phishing or malware attacks.
To mitigate this, have dedicated devices to handle social media initiatives, enable two-factor authentication, and use mobile device management (MDM) software that can wipe out data from devices in case they get lost or stolen.
#5. Not factoring in human error and insider threats
Your employees will always be the weakest link in your business’s cybersecurity. A study by PriceWaterhouseCoopers found that employees are more likely to cause cybersecurity incidents than hackers. You can take advantage of security solutions such as antivirus and firewalls, but one mistake is all it takes to jeopardize your cybersecurity.
To illustrate, an employee handling your social media may click on a phishing link, interact with a fraudulent account, or download malware. Cybercriminals are even taking advantage of the COVID-19 pandemic to launch social engineering attacks, so you have to be twice as careful. Disgruntled employees, meanwhile, may use your social media accounts to post negative comments about your company or upload inappropriate media.
Limiting access to your social media accounts is a good way to keep them secure. You may have a whole team working on social media advertising, customer service, and post creation, but not all of them should have the ability to post. Only select people should be able to post on your accounts. And when they leave your company, their access should be revoked accordingly. Perform security awareness training regularly to ensure that your employees know how to protect themselves from threats.
Don’t let these social media mistakes damage your business’s cybersecurity. Fidelis offers a full suite of managed security solutions that prevent, detect, and respond to even the most sophisticated threats. If you need foolproof cybersecurity for your Seattle or Oregon business, we are the company for you. Download our FREE cybersecurity eBook today to learn more about how we can help you.